Este conteúdo não está disponível em sua língua ainda.
Human Interaction Signature
The Human Interaction Signature (HIS) is a feature in ALTCHA Sentinel that detects automated environments and bots by analyzing user interaction events during verification. It adds an additional layer of protection, helping to identify automation and ensure interaction uniqueness across verification attempts.
Overview
HIS enhances verification by:
- Estimating automation probability based on real user interactions
- Generating an interaction signature to prevent reuse of human-like behavior across verification attempts
- Increasing internal penalty based on automation probability, resulting in higher PoW difficulty
How It Works
Automation Probability
HIS analyzes interaction signals collected during verification, such as:
- Pointer and touch movement
- Page scrolling
- Element focus and navigation
These signals are evaluated for patterns typical of genuine human behavior, which are difficult to reproduce algorithmically. Based on this analysis, HIS assigns an automation probability indicating how likely the interaction originates from a bot.
This probability contributes to the internal penalty score, which increases the difficulty of the Proof-of-Work (PoW) challenge. In stricter configurations, high automation probability may also result in the verification being blocked.
Interaction Signature
In addition to scoring, HIS generates an interaction signature — a derived hash of interaction characteristics such as timing, sequence, and movement patterns.
This signature is used to detect and prevent reuse of recorded or replayed human interactions. Depending on the configuration, repeated signatures may be rejected, and verification attempts blocked.
Enabling HIS
HIS is available from ALTCHA Sentinel version 1.25.0 onward and requires:
- PoW Version v2
- ALTCHA Widget v3
To enable HIS:
- In the Security Group configuration, set PoW Version to v2
- In the Human Interaction Signature section, select a protection mode:
RelaxedorStrict - Ensure your site integrates ALTCHA Widget v3
Modes of Protection
Both modes adjust PoW difficulty and can trigger the code-challenge based on automation probability, but differ in how strictly they enforce verification.
-
Relaxed
A friction-based approach. Increases difficulty for suspicious interactions but does not block them outright. Limited reuse of interaction signatures is allowed to reduce friction for legitimate users. -
Strict
An enforcement-based approach. Blocks verification attempts with automation probability ≥ 80% and rejects any reuse of interaction signatures.
| Mode | Blocks Automation | Allows Reuse |
|---|---|---|
| Relaxed | No | Max. 1 with low penalty |
| Strict | ≥ 80% (configurable) | No |
Choosing a Mode
- Use Relaxed for most applications, especially where accessibility and user experience are important
- Use Strict for high-risk scenarios (e.g., authentication, abuse-prone endpoints)
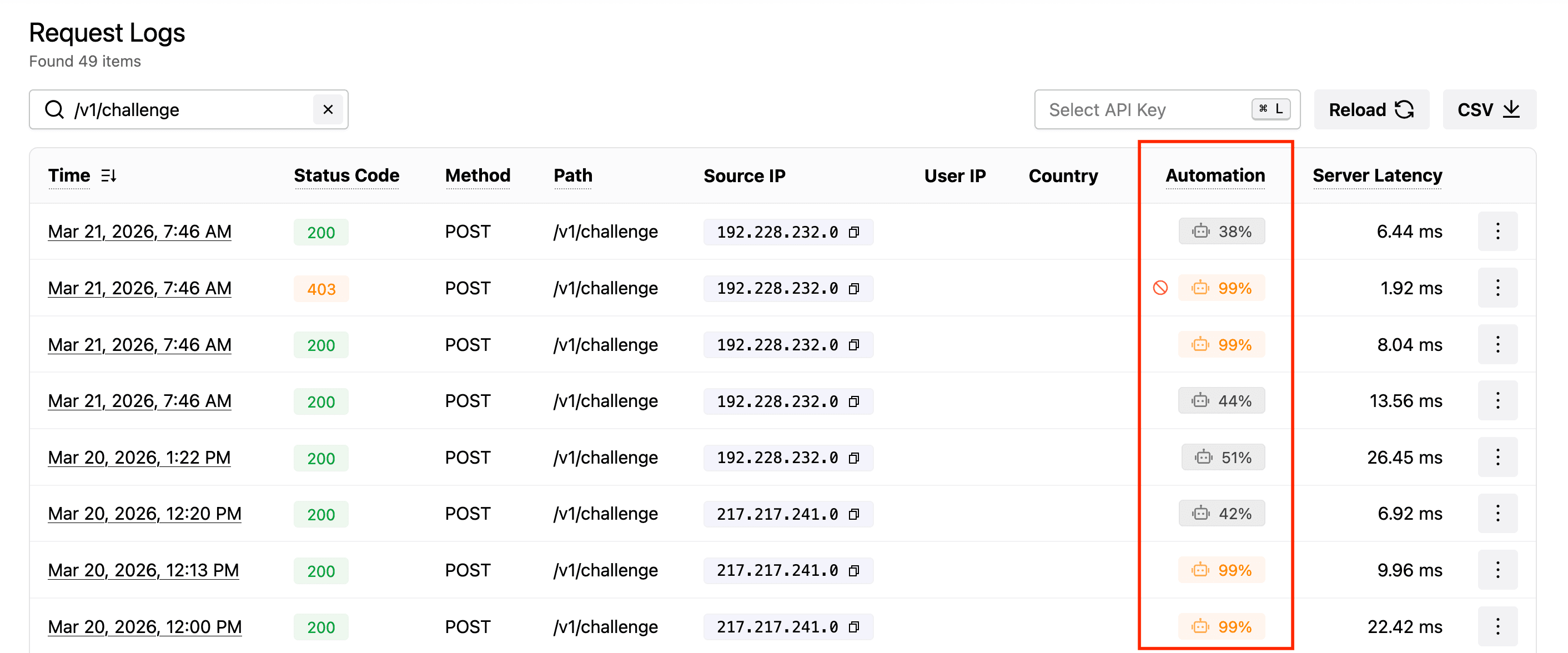
HIS may not be suitable for every website. Monitor verifications in the Logs section (under Automation) and adjust or disable HIS based on the observed scores.
Caveats
-
Requires user interaction
HIS depends on interaction data collected before verification. For best results, allow at least ~3 seconds of user interaction before triggering verification. It will not function correctly on pages that only contain the widget without interactive elements. -
Do not use with
auto="onload"
When the ALTCHA Widget is configured to auto-verify on page load, no interaction data can be collected. HIS must be disabled in this case. -
Assistive technologies
HIS correctly supports assistive technologies such as keyboard navigation. However, these interactions may result in a higher automation probability. The Relaxed mode is recommended to ensure a smooth user experience.
Technical Notes
- The duration for which a signature is stored and cannot be reused (per IP address) is configurable via the Security Group field
hisHashTTL, defaulting to12h. The actual duration is adjusted based on the automation score, with a minimum of10 min. - The block threshold for
Strictmode is configurable via thehisBlockThresholdSecurity Group field (a decimal between0and1, default0.8).